The old path
Every partner copies the same form.
Users repeat onboarding, platforms duplicate sensitive fields, and trust depends on how many databases now contain the same data.
Zero-knowledge identity orchestration
The passkey-native identity vault that turns repeated onboarding into one verified, user-controlled release.
Users keep their personal data in an encrypted vault. Partners ask for the exact fields they need. AegisVLT handles consent, cryptographic proof, and secure delivery without turning identity into another copied form.
For users
One vault for verified identity, payment, recovery, and consent.
For platforms
Lower onboarding friction without absorbing raw PII liability.
For regulated flows
Granular proof, durable audit trails, and revocable access windows.
Why it matters
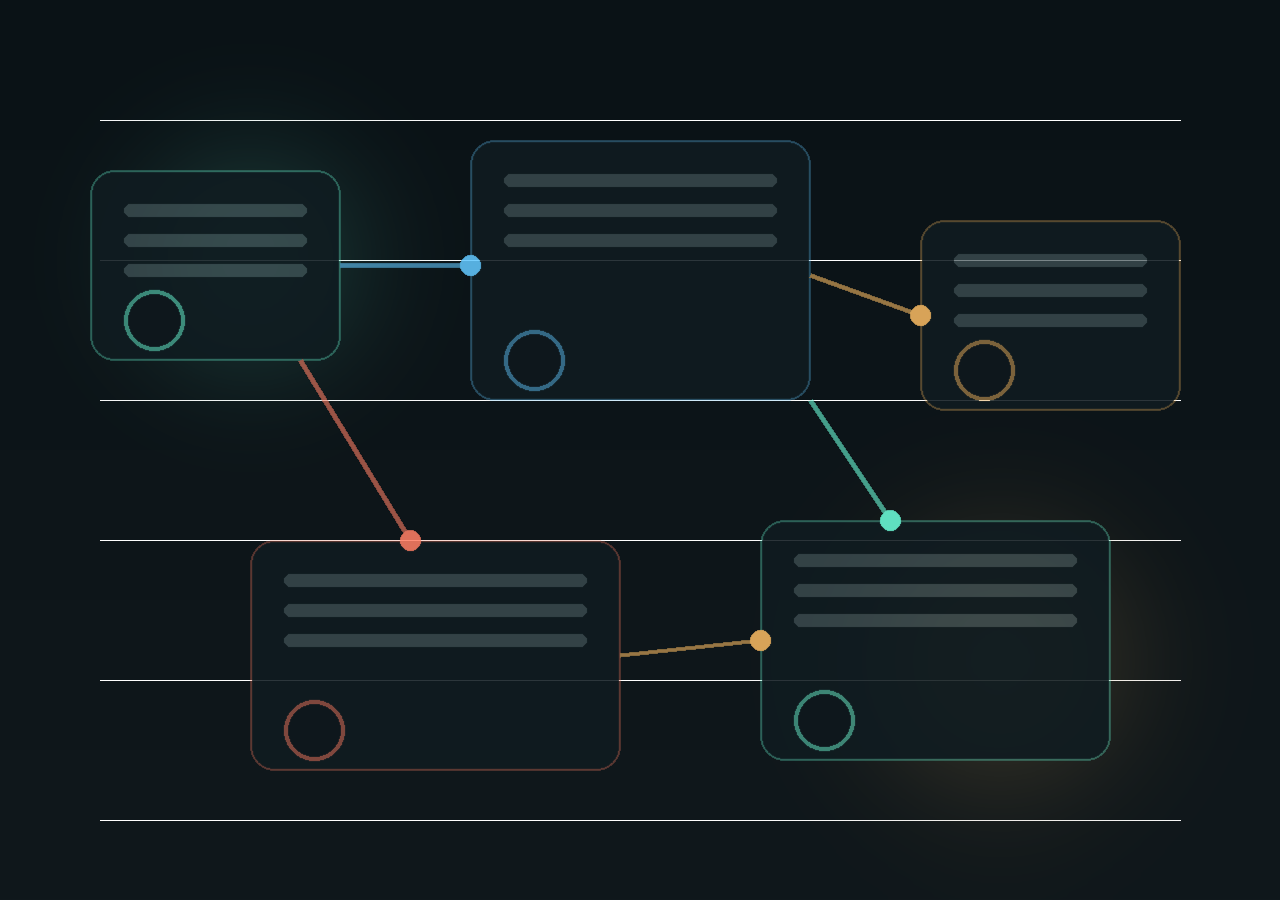
The old path
Users repeat onboarding, platforms duplicate sensitive fields, and trust depends on how many databases now contain the same data.
The AegisVLT path
The user unlocks with a passkey, approves the request, and only the selected data moves through a cryptographically verifiable channel.
The platform result
Partner apps integrate the flow once, request fewer fields, and receive structured responses that are easier to validate and audit.
Architecture
The web SDK opens a secure vault session with strict origin checks and field-level intent.
A local cryptographic release path proves user presence without turning a password into the system anchor.
The vault decrypts locally, packages the selected payload, and signs the response for the partner backend to verify.
Every access window is explicit, time-bounded, and ready for later audit.
Platform pillars
01
Encrypted blobs at rest. Decryption stays on the user side.
02
Biometric unlock replaces password reset flows and shared secrets.
03
Partners request only the attributes required for the transaction.
04
Vault orchestration runs in a separate origin with explicit messaging rules.
05
Responses are structured for signature validation and server-side trust checks.
06
Access can be logged, revoked, and reviewed without leaking raw PII.
Developer fit
AegisVLT is designed as an integration surface, not a monolith. Teams embed the web SDK, define requested claims, validate the signed response, and keep their own product flow intact.
Frontend
Launch vault sessions, request claims, and listen for approval events.
Backend
Verify response signatures before treating released identity as trusted input.
Experience
Remove long forms where verified identity already exists.
import { AegisVltClient } from "@aegisvlt/web-sdk";
const client = new AegisVltClient({
partnerId: "viseon-checkout",
mode: "production"
});
await client.openVault({
requestId: "checkout-2026-001",
fields: ["fullName", "email", "country", "over18"]
});Trust model
Release requests are explicit, bounded, and anchored to a user action.
Responses arrive in a format ready for server-side verification and policy checks.
Consent history, access scope, and recovery decisions stay legible to operators.
A new default for onboarding